Once you have installed DirectAdmin you will want to setup some firewall protection for your server. DirectAdmin as standard does not include a firewall but utilises Brute Force Monitor (BFM) to detect and prevent brute force login attempts. ConfigServer Firewall (CSF) will provide additional security measures through the Login Failure Daemon (LFD) process to periodically scan your log files to protect and block IPs who attempt to brute force login attempts against your server. In additional will provide protection against .
Since CSF v13.00 the ConfigServer team have reworked the DirectAdmin UI so it displays natively within the Directadmin dashboard. The CSF dashboard provides easy management of CSF and LFD by providing a front-end GUI where you can modify configuration files and stop, start and restart the applications and check their status.
In CSF v13.01 they added reseller support and in v13.03 add the reseller UI to the dashboard. This means that your web hosting resellers can now unblock IP addresses from within CSF directly (if you enable this feature for them), this was already present within the cPanel version of CSF but recently made the jump across to DirectAdmin.
In this guide we will show you how to install CSF/LFD onto your DirectAdmin server using either an automatic or manual installation method and enable BFM to work in conjunction to protect your server against unwanted brute force attempts.
Automated CSF/LFD Installation
Firstly we will need to install the require perl packages. These may have been installed but are sometimes missed. You can install the packages using the following command:
yum install perl-libwww-perl.noarch perl-LWP-Protocol-https.noarch perl-GDGraph -y
Now we need to download the CSF installation files and enable BFM to work together. To install both CSF and enable BFM rules we will using the following command. This command is fully automated and will download the required files, unpack it, disable the firewalld service and then install CSF for you.
wget http://files.directadmin.com/services/all/csf/csf_install.sh /bin/sh ./csf_install.sh
The CSF installation will auto-whitelist your SSH port (even if running on a non standard port) and your connected IP address to ensure you do not inadvertently block yourself.
That’s it. Your server now has CSF/LFD installed working in conjunction with BFM to protect your DirectAdmin server.
Manual CSF/LFD Installation
Before we install CSF we will need to install the require perl packages. These may have been installed but are sometimes missed. You can install the packages using the following command:
yum install perl-libwww-perl.noarch perl-LWP-Protocol-https.noarch perl-GDGraph -y
Now we will need to download CSF directly from the CSF server, unpack the .tgz file and install it. We do this using the following commands:
cd /usr/src rm -fv csf.tgz wget https://download.configserver.com/csf.tgz tar -xzf csf.tgz cd csf sh install.sh
We can test CSF to ensure all features will work on your server using the following command:
perl /usr/local/csf/bin/csftest.pl
The output will look similar to the example below:
Testing ip_tables/iptable_filter...OK Testing ipt_LOG...OK Testing ipt_multiport/xt_multiport...OK Testing ipt_REJECT...OK Testing ipt_state/xt_state...OK Testing ipt_limit/xt_limit...OK Testing ipt_recent...OK Testing xt_connlimit...OK Testing ipt_owner/xt_owner...OK Testing iptable_nat/ipt_REDIRECT...OK Testing iptable_nat/ipt_DNAT...OK RESULT: csf should function on this server
If the test result says you cannot use all the features, don’t worry, the most important part is that it does not report any FATAL errors.
When installing CSF manually you will need to disable testing from the CSF configuration file located at /etc/csf/csf.conf. You can check whether testing is active or deactivated using the following command:
grep -w '^TESTING' /etc/csf/csf.conf
If the grep command returns TESTING = “0” this means it is disabled and no further action is needed. If the command returns TESTING = “1” this means that testing is active and will need to be disabled to get CSF/LFD running.
To disable testing use the following command:
perl -pi -w -e "s/TESTING = \"1\"/TESTING = \"0\"/" /etc/csf/csf.conf
Then change the TESTING = “1” line to TESTING = “0”. After enabling CSF/LFD you will need to restart the CSF service using this command:
csf -ra
Enable Compatibility between CSF/LFD and BFM
Now we will make BFM communicate with CSF/LFD to enable automatic blocking of IPs trying to use brute force techniques on our DirectAdmin server. We can do this using the automated script provided by the team over at Poralix or we can manually install the files.
Automated CSF/LFD and BFM Installation
If you want to use the automated script to install compatibility between BFM and CSF/LFD you can use the following commands:
cd ~ wget -O csf-bfm-install.sh https://raw.githubusercontent.com/poralix/directadmin-bfm-csf/master/install.sh chmod 700 csf-bfm-install.sh ./csf-bfm-install.sh
Manual CSF/LFD and BFM Installation
First we will need to create the block IP and unblock IP using the following commands:
cd /usr/local/directadmin/scripts/custom/ cp block_ip.sh block_ip.sh.bak cp unblock_ip.sh unblock_ip.sh.bak
During this process you may encounter and error saying No such file or directory, if you do don’t panic the following commands will create the files needed.
Now we need to fetch the block IP and unblock IP files from the DirectAdmin servers using the following command:
cd /usr/local/directadmin/scripts/custom/ wget -O block_ip.sh http://files.plugins-da.net/dl/csf_block_ip.sh.txt wget -O unblock_ip.sh http://files.plugins-da.net/dl/csf_unblock_ip.sh.txt wget -O show_blocked_ips.sh http://files.plugins-da.net/dl/csf_show_blocked_ips.sh.txt chmod 700 block_ip.sh show_blocked_ips.sh unblock_ip.sh
Now we will need to create the empty blocked IP and exempt IP files using the following command:
touch /root/blocked_ips.txt touch /root/exempt_ips.txt
After you have fully tested the configuration so far to ensure you do not accidentally block your own IP, we will install the files needed for automatic blocking. To do this just use the following commands:
cd /usr/local/directadmin/scripts/custom wget -O brute_force_notice_ip.sh http://files.directadmin.com/services/all/brute_force_notice_ip.sh chmod 700 brute_force_notice_ip.sh
Configure BFM Settings in DirectAdmin
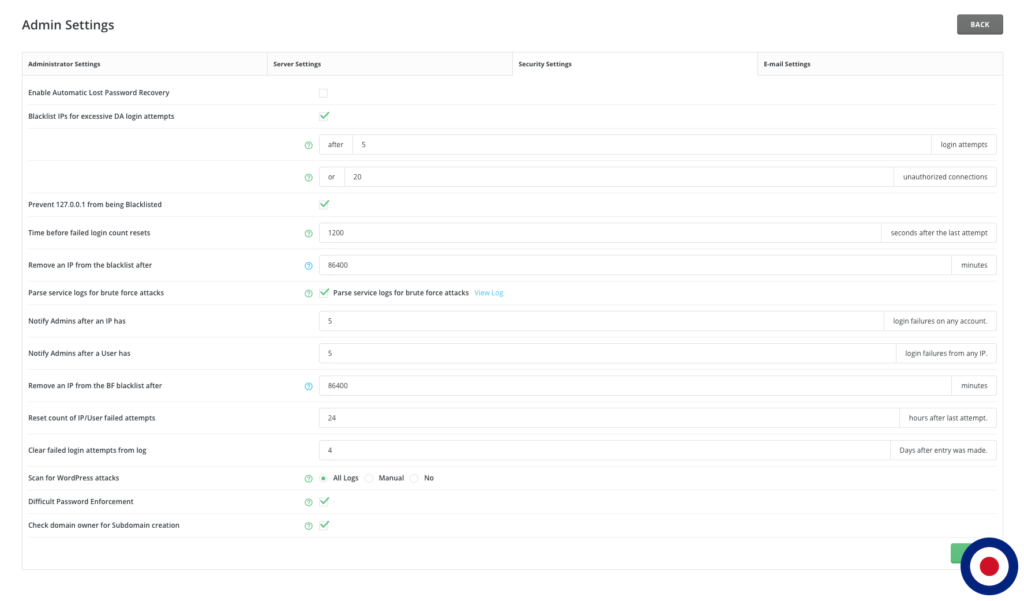
Now we will need to adjust some settings in the DirectAdmin dashboard. Just log into your DirectAdmin server and navigate to Server Manager > Adminstator Settings > Security Settings and you will be presented with the options below.
Here you can enable various settings to control BFM within DirectAdmin. You can adjust the blacklist IP settings after X amount of attempts or after X amount of connections. You will need to ensure that the checkbox Parse service logs for brute force attacks options is ticked. This will ensure DirectAdmin scans your service logs looking for brute force attempts made against Dovecot, Exim, ProFTP, SSH, etc.
Once you have made any changes required simply click the SAVE button for the changes to take effect. Now DirectAdmin’s BFM which will automatically block IPs using CSF.
Disable BFM Notification Messages
By default BFM will email you about any brute force attempts made. If you wanted to disable these message you can suppress them by making changes to your directadmin.conf file. To do this just following these commands:
echo "hide_brute_force_notifications=1" >> /usr/local/directadmin/conf/directadmin.conf service directadmin restart
Configure Block IP Script
The block_ip.sh script will automatically block an IP using iptables via CSF if the following conditions are met:
- BFM is enabled in DirectAdmin and configured.
- CSF/LFD is installed together with the scripts above to allow DirectAdmin to communicate with CSF.
- IP exceeded max allowed number of login failures on any account.
- IP is missing in brute force skip list (/usr/local/directadmin/data/admin/brute_skip.list).
- IP is not white-listed in CSF permanently (/etc/csf/csf.allow). Any mention of an IP in the csf.allow will protect the IP from blocking.
- IP is not temporary in allowed list of CSF (/var/lib/csf/csf.tempallow).
The IP addressed will be blocked from accessing either the port which was attacked or you can block access to all ports on your server. The block_ip.sh script uses a USE_PORT_SELECTED_BLOCK to mange this option. The default setting is USE_PORT_SELECTED_BLOCK=1 which means the ban will only apply to the port which was attacked. However, you can change this setting by editing the following file:
nano /usr/local/directadmin/scripts/custom/block_ip.sh
At the top of the file change the USE_PORT_SELECTED_BLOCK switch from 1 to 0.
USE_PORT_SELECTED_BLOCK=0; # SET TO 1 OR 0
# 1: TO BAN ACCESS ONLY TO A PORT WHICH
# WAS BRUTEFORCED
# 0: TO BLOCK ACCESS TO ALL PORTS
#
# NOTICE: MANUAL TRIGGER FROM DIRECTADMIN
# WILL STILL BLOCK ACCESS TO ALL PORTS
# FOR AN IPYou can also use the block_ip.sh file to update the port lists if you have changed the default ports used by DirectAdmin, FTP or SSH.




4 Comments for How to Install ConfigServer Firewall (CSF) and Brute Force Monitor (BFM) with DirectAdmin
Great article! Thanks!
Hi Julio
Thank you for the feedback and we are glad you found the guide useful.
Kind Regards
VPSBasics
what if i have pfsense over the top of DA vmachine? should i install csf yet?
Hi Alexis
Not too familiar with pfSense but as I understand it couldn’t you just set the firewall rules and settings within pfSense for the VM at router/server level.
Also, are you using FreeBSD as I don’t believe you can use CSF with that OS either because it doesn’t support iptables.
Kind Regards
VPSBasics